Cyber Security Blog of Chris Dale
-

Simple XSS Cookie Stealer
Just wanted to share a simple XSS cookie stealer that I like to use for demos. Primarily I put this into a post because I’ve seen many use the document.location in their payloads, but this will cause victim browser to be redirected to attacker, which is not very nice (not stealthy). Put the following in…
-
The Hacker Manifesto
As a hacker, I am driven by a relentless curiosity and a desire to uncover the hidden truths that lie just beyond our reach. I know that there is always a way to penetrate even the most seemingly impenetrable systems. I approach every challenge with sharp senses, a keen intellect, and an open mind, ready…
-

Deception Concepts – Elements of Deception
Deception is not reserved only for the attackers. Defenders can play the deceptive game too, and it can be game changing! Here are some abstractions that are useful to consider during deception planning NEDI Nonessential elements of deceptive information (NEDI): Fictional information that is to be hidden. Information we can share with attackers, but not…
-

PowerShell Profile
PowerShell is a bit awkward to begin with. See my YouTube video on how to start learning PowerShell. It walks through the most important commands to know about, hopefully allowing you to kick start your PowerShell career. See below for my simple PowerShell profile and why you should consider yours. PowerShell Profile The profile file…
-

Personal Mission Statement
Having a mission statement is important, especially a personal one! Consider this as a short and personal message to everyone else seeking: who am I, what am I and what am I to achieve? Live life to the fullest. Be a character which is looked upon, respected for wits and fun, and someone people will…
-

Offensive SOC, Attack Surface Management and Always-On Pentesting
New topics for many: Offensive Security Operations Center, Attack Surface Management and Always-On penetration testing! What are these concepts? How can attackers leverage opportunities to show risk continuously instead of on a snapshot basis? Learn more in my webcast on the topic:
-

I’ve established a new company!
I am very proud! Last week, Magnus Holst and me established a new company, River Security. Check out our mission and services here: https://riversecurity.eu
-

Docker for Information Security Professionals
I just did a webcast on this topic. It has slides and examples on how to utilize Docker for security related work. I hope you enjoy!
-
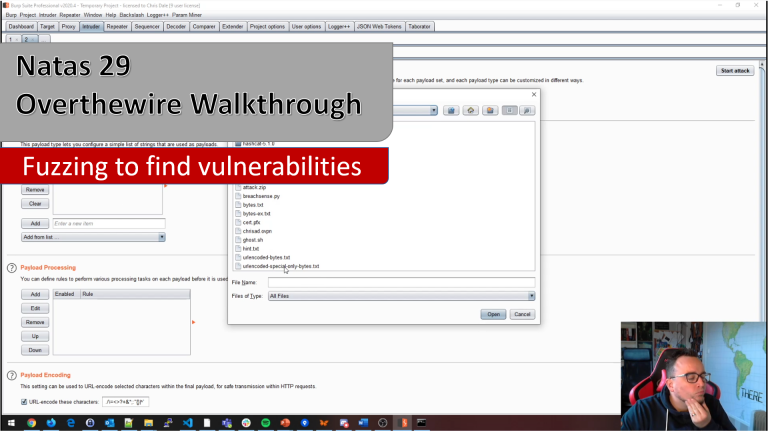
YouTube video release – Fuzzing for vulnerabilities
Fuzzing and figuring out where vulnerabilities might be is an essential skill for anyone looking to discover vulnerabilities.
-
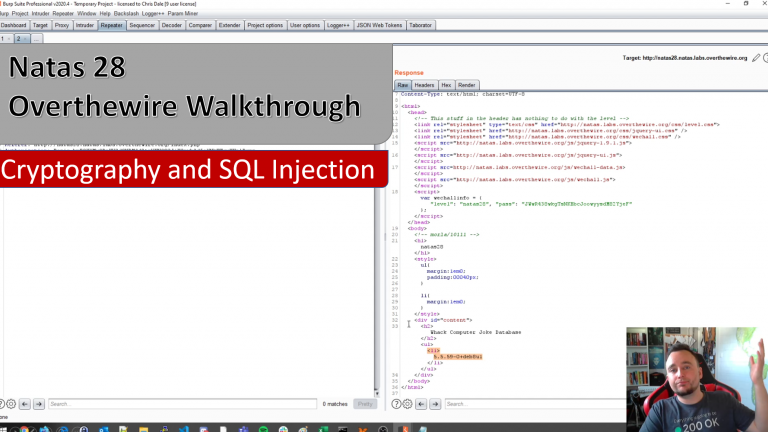
YouTube video release – Breaking ECB Crypto (No programming)
Cryptography is not always deployed in a secure manner. When user controlled input is provided to a server and the server encrypts the data, outputting the results back to the user, it might be used as an oracle to learn which plain-text provide which encrypted data. This weakness is often present in Electronic Code Book…
Looking to get in touch?